Ransomware Landscape Shifts: Dominant Groups Tighten Grip in Q1 2026
Breaking: Ransomware Attack Volume Stabilizes at High Levels as Top Groups Consolidate Power
The first quarter of 2026 has seen a sharp reversal in the ransomware threat landscape, with the top 10 criminal groups now responsible for 71% of all publicly posted victims—the highest concentration since early 2024, according to new data released today.

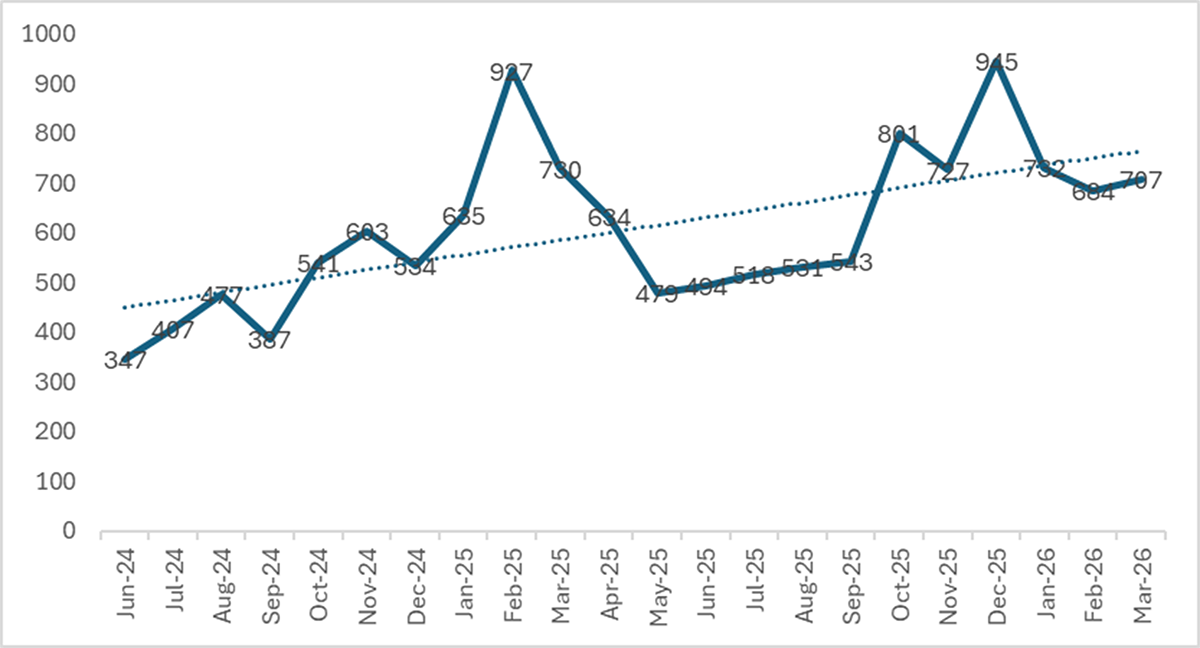
Overall, 2,122 victims were listed on data leak sites (DLS) between January and March, making it the second-highest Q1 on record. While this represents a 12.2% decline from the all-time record set in Q4 2025 (2,416 victims), the volume remains 117% above Q1 2024 levels, indicating a sustained threat.
"The consolidation we're seeing is a major structural shift. After two years of fragmentation, the ecosystem is once again coalescing around a few dominant players—and that makes tracking and defending against them more challenging," said Dr. Elena Rossi, Senior Cyber Threat Analyst at Collective Defense Labs.
Background: Fragmentation Reversal
From mid-2024 through late 2025, the ransomware ecosystem fragmented rapidly. The number of active groups swelled from 51 in Q1 2024 to a peak of 85 in Q3 2025. During that period, the top 10 groups' share of victims fell from 68% to just 57%.
That trend has now reversed. In Q1 2026, the number of active groups dropped to 71, with 14 groups disappearing entirely and 21 new ones emerging. The top 10 now control 71.1% of all DLS-posted victims.
"This consolidation is reminiscent of the post-Conti era. When a few big players dominate, they can share infrastructure and tactics more efficiently—making them harder to disrupt," noted James Kowalski, former FBI cybercrime investigator and current advisor at ThreatHorizon.
The Key Players in Q1 2026
- Qilin maintained its top spot for the third consecutive quarter, posting 338 victims.
- The Gentlemen surged to third place with 166 victims, up from just 40 in Q4 2025—a 315% increase.*
- LockBit 5.0 confirmed its comeback with 163 victims, placing fourth.
- The top 10 collectively accounted for over 1,500 victims.
Monthly victim counts remained remarkably stable: 732 in January, 684 in February, and 706 in March—an average of 707 per month.
What This Means for Cybersecurity
The headline year-over-year comparison shows a 7.1% decline from Q1 2025 (2,285 victims). However, that figure is misleading. Q1 2025 was inflated by Cl0p’s Cleo mass-exploitation campaign, which alone contributed roughly 390 victims.
Excluding Cl0p from both periods, the true YoY change is an increase of 5.3%—from 1,894 victims in Q1 2025 to 1,995 in Q1 2026. This suggests the underlying growth trend in ransomware operations continues, even as dramatic spikes subside.
"Organizations should not be lulled by the slight Q4-to-Q1 drop. The baseline is still alarmingly high, and the consolidation means that a single takedown—like Qilin or LockBit—could temporarily shake the ecosystem, but others will quickly fill the gap," warned Sarah Nguyen, Principal Threat Intel Analyst at Securosis.
Experts advise that businesses focus on fundamentals: patch management, network segmentation, and robust backup strategies—especially for critical infrastructure sectors that remain prime targets.
This article is based on data from active data leak site monitoring. The full report is expected next week.
Related Articles
- Deploy AI Agents with Amazon WorkSpaces: A Step-by-Step Setup Guide
- Decoding Semantic Search: A Practical Guide to Vector Databases vs. Traditional Text Search
- Quantum-Proof Ransomware Confirmed: Kyber Uses NIST-Approved Encryption to Evade Future Decryption
- Unlocking Japan's Genetic Past: A Step-by-Step Guide to the New Third Ancestry Discovery
- Demystifying Word2vec: What It Really Learns and How
- How to Experience 50 Years of Space History at NASA Goddard’s Visitor Center
- Baltic Wader Nest Conservation: When to Intervene Against Storm Floods – A Practical Guide
- Flight Research at NASA Armstrong: 10 Key Developments and Capabilities